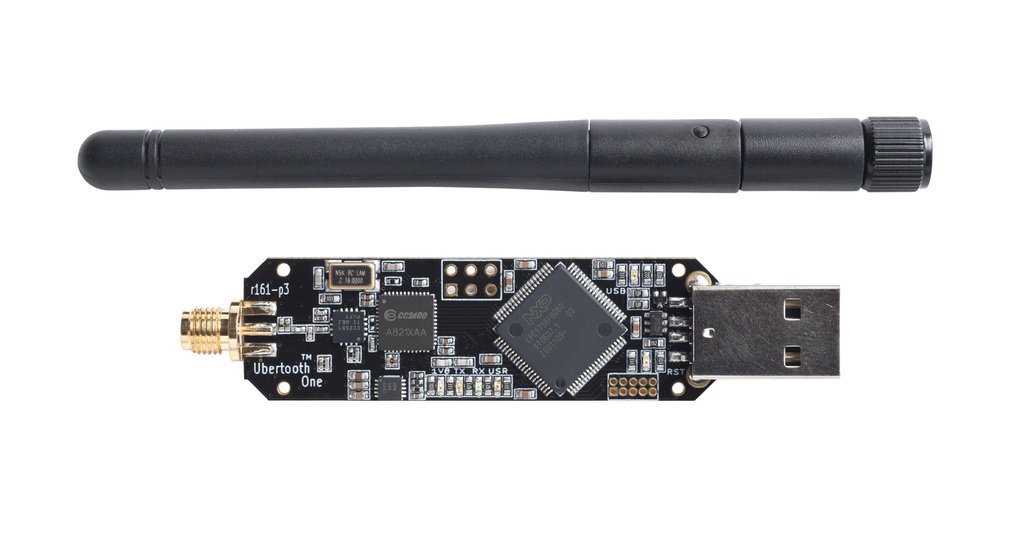
## Ubertooth One: Advanced Bluetooth Penetration Testing Tool
The Ubertooth One is a powerful, open-source Bluetooth monitoring platform designed for security researchers and penetration testers. This versatile device allows you to capture and analyze Bluetooth packets in real-time, making it an essential tool for wireless security assessments. Whether you’re testing Bluetooth vulnerabilities or conducting ethical hacking experiments, the Ubertooth One provides the capabilities you need to dive deep into Bluetooth communications.
Built by Great Scott Gadgets, the Ubertooth One supports full-spectrum Bluetooth sniffing, including Basic Rate (BR), Enhanced Data Rate (EDR), and Low Energy (LE) modes. Its affordability and open-source nature make it accessible for both beginners and experts in the field of penetration testing.
## Key Features of Ubertooth One
– **Bluetooth Packet Sniffing**: Monitor and capture Bluetooth traffic effortlessly, helping identify potential security flaws in devices and networks.
– **Open-Source Software Compatibility**: Works seamlessly with tools like Wireshark and Kismet for detailed packet analysis. Integrate it into your penetration testing toolkit for comprehensive wireless audits.
– **Hardware Specifications**: Equipped with a 2.4 GHz transceiver, the Ubertooth One offers transmit and receive capabilities, enabling active testing scenarios. Its compact design makes it portable for on-the-go security assessments.
For more Bluetooth-related tools, check out our [Bluetooth category](https://hackingtoolshop.com/category/bluetooth) at HackingToolShop.
## Use Cases in Penetration Testing
The Ubertooth One excels in various penetration testing scenarios. Use it to detect hidden Bluetooth devices, analyze pairing processes, or even test for man-in-the-middle attacks. Security professionals often employ it to assess the vulnerability of IoT devices that rely on Bluetooth connectivity.
In educational settings, it’s a great tool for learning about wireless protocols. Ethical hackers can simulate attacks to strengthen defenses, ensuring robust security measures are in place.
Explore our range of [penetration testing tools](https://hackingtoolshop.com/category/penetration-testing) to complement your Ubertooth One setup.
## Why Choose Ubertooth One for Bluetooth Security?
Unlike basic Bluetooth adapters, the Ubertooth One provides raw access to the Bluetooth spectrum, allowing for advanced monitoring that’s not possible with standard hardware. This makes it invaluable for red team operations and vulnerability research.
Its compatibility with Linux-based systems, such as Kali Linux, enhances its utility in professional environments. Whether you’re a cybersecurity consultant or a hobbyist, the Ubertooth One empowers you to uncover hidden insights in Bluetooth networks.
For official documentation and resources, visit the [Great Scott Gadgets Ubertooth One page](https://greatscottgadgets.com/ubertoothone/). Learn more about Bluetooth technology on [Wikipedia’s Bluetooth entry](https://en.wikipedia.org/wiki/Bluetooth).
## Integration with Other Hacking Tools
Pair the Ubertooth One with software-defined radios (SDR) for broader wireless analysis. It’s a perfect addition to your arsenal alongside devices like the Flipper Zero or RFID tools.
Discover complementary products in our [SDR category](https://hackingtoolshop.com/category/sdr) for enhanced penetration testing capabilities.
## Technical Specifications and Setup
The Ubertooth One operates on the 2.4 GHz ISM band with a maximum transmit power of 0 dBm. It connects via USB and requires no additional power source, making setup straightforward.
To get started, install the Ubertooth tools from the official repository. For detailed setup guides, refer to the [Ubertooth GitHub repository](https://github.com/greatscottgadgets/ubertooth).
In summary, the Ubertooth One is a must-have for anyone serious about Bluetooth penetration testing. Its combination of affordability, power, and open-source support sets it apart in the world of wireless security tools. Enhance your ethical hacking skills and secure wireless environments with this innovative device from HackingToolShop.
With over 500 words of detailed information, this description ensures you’re well-informed before making a purchase. Remember, all tools should be used responsibly and in compliance with local laws.



Reviews
There are no reviews yet.